Filter by
SubjectRequired
LanguageRequired
The language used throughout the course, in both instruction and assessments.
Learning ProductRequired
LevelRequired
DurationRequired
SkillsRequired
SubtitlesRequired
EducatorRequired
Results for "security testing techniques"

Skills you'll gain: Network Security, Intrusion Detection and Prevention, Hardening, TCP/IP, Cyber Attacks, Network Architecture, Computer Networking, Cloud Computing, Firewall, Network Infrastructure, Network Protocols, Virtual Private Networks (VPN)
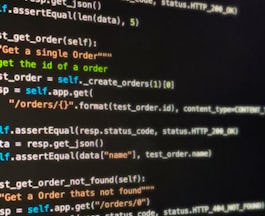
Skills you'll gain: Test Driven Development (TDD), Gherkin (Scripting Language), Code Coverage, Behavior-Driven Development, Software Testing, Unit Testing, Test Automation, Test Tools, Test Case, Test Data, Restful API, Microservices

Skills you'll gain: Malware Protection, Computer Security Awareness Training, Security Awareness, Mobile Security, Network Security, Data Security, Cyber Attacks, Cybersecurity, Human Factors (Security), Email Security, Identity and Access Management, Multi-Factor Authentication, Authentications
 Status: [object Object]
Status: [object Object]Microsoft
Skills you'll gain: Threat Modeling, MITRE ATT&CK Framework, Penetration Testing, Azure Active Directory, Network Security, Computer Systems, Security Information and Event Management (SIEM), Security Testing, Encryption, Cybersecurity, Cyber Security Strategy, System Testing, Cloud Security, Threat Management, Cloud Computing, Business Software, Cyber Attacks, Authentications, Active Directory, Data Management

Skills you'll gain: Open Web Application Security Project (OWASP), Security Controls, Risk Management, Cybersecurity, Security Information and Event Management (SIEM), Incident Response, NIST 800-53, Cyber Security Policies, Cyber Risk, Safety Audits, Threat Detection, Compliance Auditing
 Status: Free
Status: FreeErasmus University Rotterdam
Skills you'll gain: Security Management, Threat Management, Intelligence Collection and Analysis, International Relations, Public Safety and National Security, Security Awareness, Risk Management, Threat Detection, Governance, Law, Regulation, and Compliance, Innovation, Policy Development
 Status: [object Object]
Status: [object Object]Google
Skills you'll gain: Storyboarding, Wireframing, UI/UX Research, Responsive Web Design, User Experience Design, Design Thinking, User Research, Information Architecture, Figma (Design Software), Usability Testing, User Story, Web Design, Design Reviews, Usability, Presentations, Design Research, Persona (User Experience), Ideation, User Centered Design, Mockups
 Status: [object Object]
Status: [object Object]Microsoft
Skills you'll gain: Data Storytelling, Dashboard, Excel Formulas, Extract, Transform, Load, Power BI, Data Analysis Expressions (DAX), Microsoft Excel, Data Modeling, Data-Driven Decision-Making, Star Schema, Data Analysis, Data Presentation, Data Visualization Software, Microsoft Power Platform, Data Integrity, Spreadsheet Software, Data Validation, Data Transformation, Data Cleansing, Data Visualization
EC-Council
Skills you'll gain: Penetration Testing, Threat Management, Distributed Denial-Of-Service (DDoS) Attacks, Cloud Security, Vulnerability Assessments, Network Security, Threat Detection, Vulnerability Scanning, Security Awareness, Cyber Threat Intelligence, Cybersecurity, Intrusion Detection and Prevention, Cyber Attacks, Application Security, Web Applications, Mobile Security, Internet Of Things, Authentications, Encryption, Wireless Networks

Skills you'll gain: Linux Commands, Linux, Penetration Testing, Open Web Application Security Project (OWASP), Vulnerability Scanning, Security Testing, Scripting, Vulnerability Assessments, Scripting Languages, Intrusion Detection and Prevention, General Networking, Python Programming, Network Security, Cybersecurity, Firewall, Application Security, Web Applications, Cyber Operations, Data Ethics, Computer Programming

Skills you'll gain: Network Security, Incident Response, Security Controls, Business Continuity, Disaster Recovery, Information Assurance, System Configuration, Configuration Management, Cybersecurity, Security Awareness, Security Management, Computer Security Incident Management, Cyber Attacks, Data Security, Infrastructure Security, Risk Management Framework, Event Monitoring, Encryption, Role-Based Access Control (RBAC), Authorization (Computing)

Skills you'll gain: Cybersecurity, Encryption, Cyber Attacks, Email Security, Computer Security Awareness Training, Security Awareness, Data Security, Information Systems Security, Malware Protection, Authentications, Authorization (Computing), Security Controls, Hardening, Identity and Access Management, Multi-Factor Authentication, Browser Compatibility
In summary, here are 10 of our most popular security testing techniques courses
- Connect and Protect: Networks and Network Security: Google
- Introduction to Test and Behavior Driven Development: IBM
- Security Awareness Training: ISC2
- Microsoft Cybersecurity Analyst: Microsoft
- Play It Safe: Manage Security Risks: Google
- International Security Management: Erasmus University Rotterdam
- Google UX Design: Google
- Microsoft Power BI Data Analyst: Microsoft
- Ethical Hacking Essentials (EHE): EC-Council
- The Complete Ethical Hacking Bootcamp: Beginner To Advanced: Packt










